Organizations must take proactive measures to protect their sensitive data and systems. Malicious actions, whether carried out by external attackers or insider threats, can result in financial losses, reputational damage, and regulatory penalties.
To stay ahead, organizations need a comprehensive defense strategy that combines technology, policies, and employee awareness. Here’s how you can control access to privileged accounts, the primary targets for attackers.
Privileged Access Management Solutions
Privileged accounts provide users with elevated permissions to perform sensitive tasks, including configuring systems, accessing confidential data, or managing security settings. Know that understanding privileged access management solutions for any organization seeking to secure its IT environment. Misuse of these accounts can have devastating consequences.
These solutions help organizations monitor, control, and audit privileged accounts. By limiting access to only what is necessary and tracking all activities, organizations can decrease the likelihood of data breaches. Advanced privileged access management tools include session recording, automated password rotation, and real-time alerting, which add layers of protection against malicious activity.
Implementing Role-Based Access Control
Role-based access control (RBAC) assigns permissions based on a user’s role within the organization rather than providing unrestricted access. RBAC aligns privileges with job responsibilities and minimizes the risk of unauthorized access.
RBAC simplifies the process of onboarding and offboarding employees. When a user changes roles or leaves the organization, their access rights can be updated or revoked systematically. This reduces the risk of leftover accounts being exploited. Role-based access policies provide clarity and accountability, making it easier to track who accessed what and when.
Enforcing Strong Authentication Mechanisms
Weak or compromised passwords are a common vector for cyberattacks, so organizations should implement strong authentication mechanisms. Multi-factor authentication (MFA), biometric verification, and hardware security keys are all effective methods so that only authorized users can access sensitive resources.
MFA requires users to provide multiple forms of verification, including a password and a one-time code sent to a mobile device. Organizations should regularly review authentication policies so that they are aligned with evolving threats.
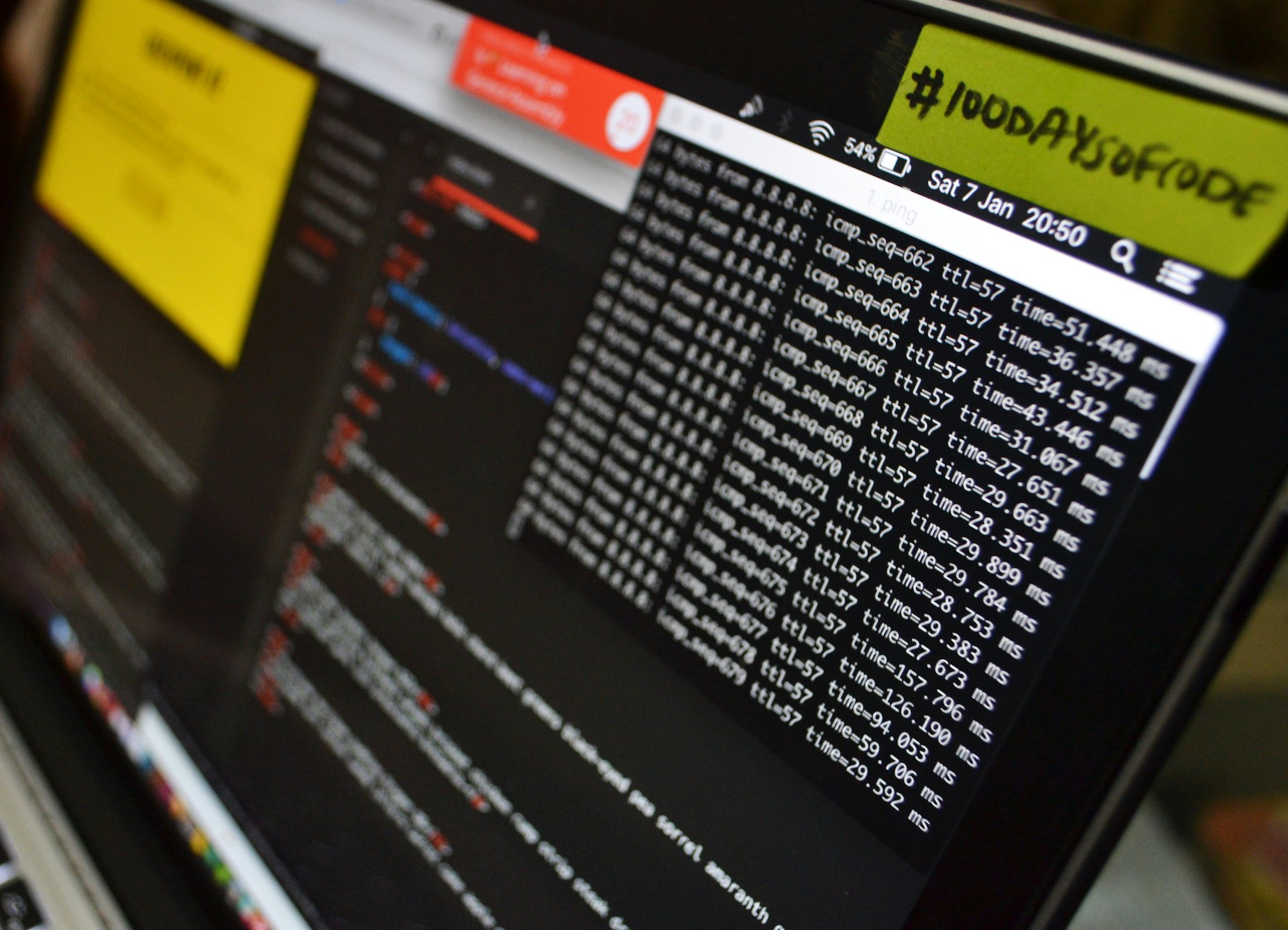
Monitoring and Logging Privileged Activities
Even with strict access controls in place, malicious actions can still occur. Continuous monitoring and logging of privileged activities help organizations detect suspicious behavior early. Detailed logs allow security teams to identify anomalies, investigate potential breaches, and respond quickly to threats.
Monitoring tools can alert administrators to unusual activity in the form of unauthorized login attempts or changes to critical system configurations. These logs are invaluable for forensic investigations and regulatory compliance. By maintaining a clear record of privileged activities, organizations can demonstrate that they are taking steps to protect sensitive assets.
Filtering Content to Stop Malware
Most attacks start with a bad link or a fishy file sent to an employee. Controlling what enters your network is a great way to lower your risk. You can stop malicious content by using filters to only allow the types of files you expect. Blocking websites that are known to be dangerous keeps your staff from making a mistake.
Malware hides in plain sight within common file formats. By setting rules for what can be downloaded, you take away a common tool for hackers. If your office only uses spreadsheets and text files, there is no reason to allow other risky formats.
Web filtering prevents users from landing on sites that host harmful scripts. These sites may work in the background to steal info. A good filter checks the reputation of a site before the page even loads. Using these tools makes your defense much more reliable.
Conducting Regular Security Audits
Regular security audits can identify vulnerabilities, misconfigurations, and policy gaps that could be exploited by malicious actors. Conducting routine assessments can continuously improve the business’s security posture and reduce the risk of breaches.
Audits should cover technical controls, policies, and procedures related to access management. Verifying that privileged accounts are correctly provisioned, inactive accounts are disabled, and access requests follow proper approval processes can prevent potential security incidents. Organizations that adopt a proactive audit strategy are better prepared to withstand attacks.
Educating Employees on Security Awareness
Human error remains one of the leading causes of security breaches. Employees who are unaware of security best practices can inadvertently become the weakest link in an organization’s defense. Educating staff on recognizing phishing attempts, using secure passwords, and reporting suspicious activity is required.
Security awareness programs should be ongoing and include practical exercises, including simulated phishing attacks and training sessions on proper data handling. When employees understand the role they play in maintaining security, organizations can decrease the risk of insider threats and accidental data exposure.
Managing System Updates and Patches
Software always has bugs that could be used by attackers. Companies release updates to fix these holes as soon as they find them. If you do not install these updates, your system stays vulnerable. Keeping your software current is a basic task that many people ignore.
Automated updates can make this job much easier for a busy team. You can set your computers to download and install patches overnight. This way, you are always running the safest version of your tools and preventing hackers from using known flaws to get inside your network.
Old software that is no longer supported is a big risk. If a company stops making updates, any new bugs will never be fixed. It is best to move away from these end-of-life products as soon as possible. Replacing old tech with newer, safer versions keeps your defenses strong and avoids the cost of a major data breach later.
Training Staff to Spot Phishing Attempts
Employees are the target of social engineering attacks. Hackers send emails that look like they come from a boss or a bank, and these messages try to trick people into giving away their login details. A few key signs of a phishing email include:
- Urgent or threatening language that demands quick action
- Links that do not match the official website of the sender
- Strange email addresses that are slightly misspelled
- Requests for sensitive info like passwords or wire transfers
- Attachments that you were not expecting to receive
Interactive training sessions keep these lessons fresh in everyone’s mind. You can even run fake phishing tests to see how people react. These tests show you where you might need more training. When people feel confident in their ability to spot a scam, they are less likely to fall for one.
Bad actors change their tactics all the time. Sharing news about the latest tricks keeps the team alert and builds a sense of shared responsibility for the company’s safety. When everyone is looking out for the group, the risk of a successful attack goes down.
Utilizing Advanced Threat Detection Technologies
Technology defends against malicious actions. Advanced threat detection solutions like intrusion detection systems (IDS), endpoint detection and response (EDR), and security information and event management (SIEM) platforms help organizations identify and respond to threats in real time.
These tools leverage machine learning and behavioral analytics to detect anomalies that may indicate an attack. A sudden spike in data downloads or unusual login patterns can trigger alerts for further investigation.
Planning For Incident Response
Even the best defenses can fail, and you need a plan for what to do when something goes wrong. An incident response plan tells everyone their role during a crisis. It helps the team stay calm and work fast to fix the problem. Having a clear set of steps can save a company from a total disaster.
Key parts of a good plan include:
- A list of people who need to be notified right away
- Steps to isolate the affected systems and stop the spread
- Methods for backing up data before you start repairs
- A plan for talking to customers and the public about the event
- A process for looking back at the incident to learn what happened
You can run tabletop exercises where the team talks through a fake hack. These drills show you where the plan might be confusing. Everyone will know exactly what to do when the clock is ticking. Being prepared makes a big difference in how much damage a hack can cause.
A good response involves forensic work. You want to know how the attacker got in, so you can stop them from doing it again. Each incident is a chance to improve your walls. A well-managed crisis can build trust with your clients if you handle it well.
Leveraging Security Best Practices
Adopting security best practices strengthens an organization’s defense against malicious actions. Key measures include:
- Regularly updating software and systems to patch vulnerabilities.
- Implementing network segmentation to limit the lateral movement of attackers.
- Encrypting sensitive data both in transit and at rest.
- Applying the principle of least privilege to minimize unnecessary access.
- Conducting employment background checks for those critical roles.
- Automating security workflows to reduce human error and response times.
These best practices, combined with technical solutions and employee training, create a multi-layered defense that makes it much harder for attackers to succeed.
Businesses that combine strong privileged access management solutions with proactive monitoring, employee education, and robust response strategies can lower the risk of malicious actions. These practices will secure their systems and build a culture of security awareness that strengthens their resilience.